Top 5 EOR Providers for Remote Companies
Managing a distributed team across different countries comes with real headaches—local tax codes, employment laws that change from one border to the n
READ MOREEmerging Browser Hijackers on macOS: Detection, Impact, and Removal Strategies
Browser hijackers targeting macOS used to look like aggressive pop-ups or obvious spam messages. It was easy to spot them, but that’s no longer the ca
READ MORECyber Risk Management Frameworks Every Organisation Should Know
Cyber threats are a growing concern for businesses of all sizes. From ransomware attacks to data breaches and phishing schemes, the potential impact o
READ MOREUnlocking Cybersecurity: Market Intelligence Tools & Trends
Cybersecurity isn't something you can ignore anymore. It doesn't matter if you're running a small local bakery or managing IT for a massive corporatio
READ MOREPost-Quantum Encryption Isn’t Tomorrow’s Problem; It’s Today’s Planning
In the ever-changing world of cybersecurity, a countdown has silently started. Although Q-Day, the point at which a quantum computer is powerful enoug
READ MOREPopuler Cyber Security Salaries Guide
A single data breach can cost a company up to $3.29 million, a 12% rise from the previous year's breaches (BM's Cost of a Data Breach research). Co
READ MORE30+ Inspirational Women in Cyber Security Industry
About a quarter of the cybersecurity workforce is comprised of women. While this is an increase from 11% in 2017, there are still significant barriers
READ MOREThe Ultimate Guide to Building a Diverse Team in Cyber Security
New ideas are needed if corporations are to establish a more robust defense against cyber-attacks. That entails creating security teams that are more
READ MOREInvestors Guide to Cyber Security Startups
The second quarter saw significant funding for cybersecurity businesses and cyber security investments despite the slowdown in venture capital. Acc
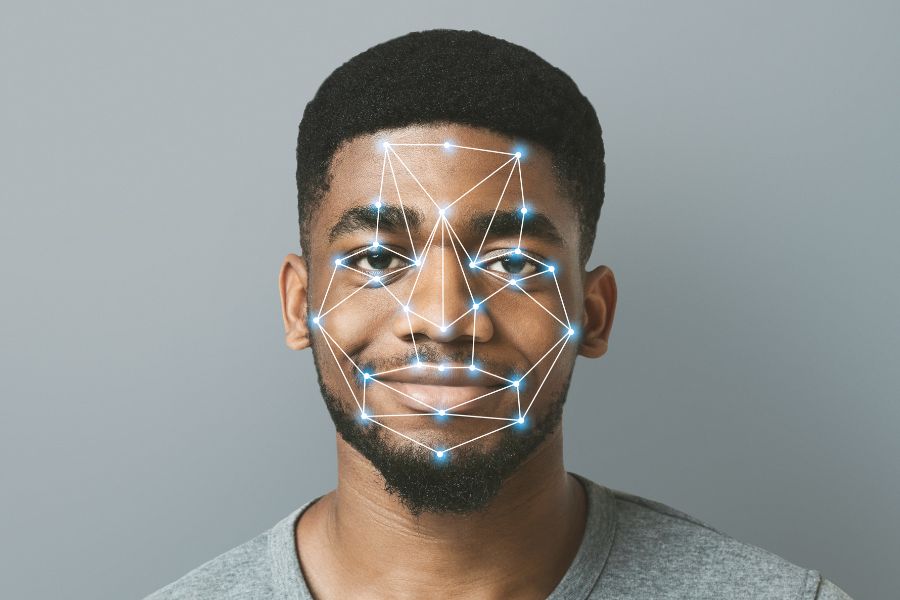
READ MOREWhat is Face Recognition – How Does it Work?
There is a comparison between the data and a library of recognised faces. Identity verification by face recognition has the potential to improve secur
READ MOREHow to Become a Great Cyber Security Architect?
You hear about another horrifying incident involving corporate cybersecurity, phishing, or internet fraud wherever you go. The prevalence of cybercrim
READ MOREWhat is an Endpoint? What’s the Goal of Endpoint Security?
Securing the access points, or endpoints, of end-user devices, including desktops, laptops, and mobile devices, from exploitation by hostile actors an
READ MORE