Cyber Security Basics
Cyber security is one of the most critical topics in today’s digital world. It involves protecting computer networks and systems from unauthorized access or damage. It also covers measures to protect data from malicious software, hackers, and other online threats. In this blog category, we will share basic tips to help you stay safe online.

Cyber Security Basics
Vulnerability Management 101: Key Steps and Strategies
Cyberattacks can affect endpoints, workloads, and systems; however, these vulnerabilities can be reduced using a vulnerability management system. As a...
READ MOREWhat are the Top Types of Authentification Methods?
The need for robust user authentication methods in both digital and analog settings is rising. User authentication can be used for everything from acc...
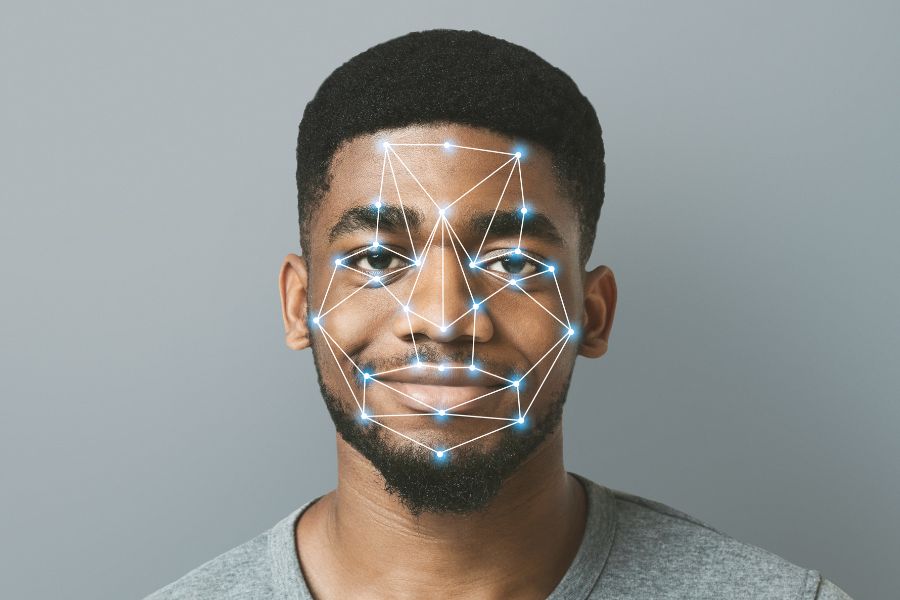
READ MOREWhat is Face Recognition – How Does it Work?
There is a comparison between the data and a library of recognised faces. Identity verification by face recognition has the potential to improve secur...
READ MOREWhat is an Endpoint? What’s the Goal of Endpoint Security?
Securing the access points, or endpoints, of end-user devices, including desktops, laptops, and mobile devices, from exploitation by hostile actors an...
READ MOREHow Can Online Credit Card Transactions Be Made More Secure?
A company can take various measures to protect its customers' personal information during online transactions. When conducting business online, follow...
READ MOREWhat are the Different Types of Firewalls in 2024?
A firewall provides an important additional layer of protection by obstructing unauthorized access to internal networks. During the past four decades,...
READ MOREMulti Factor Authentication (MFA): Definition, Types and Examples
By logging into your online accounts, also known as "authentication," you are proving to the service that you are who you say you are. A username and ...
READ MOREHow to Prevent Linkedin Data Leaks?
With data breaches becoming more common, ensuring your LinkedIn profile is secure is essential. Our guide will show you how to protect your personal i...
READ MOREWhat are The Most Common Vulnerabilities of Websites?
Websites are vulnerable to various threats, including malware, phishing, SQL injection attacks, cross-site scripting, etc. Learn more about the most c...
READ MORECommon Email Security Issues and Mistakes to Avoid in 2026
This blog post focuses on the potential threats to email security in 2026. In 2026, like in 2025, email will be a significant security issue or concer...
READ MOREWhat Makes SOC Effective? People, Process, and Technology
In today's rapidly-evolving cyber threat landscape, Security Operations Centers (SOCs) are becoming increasingly vital for organizations looking to pr...
READ MORESecurity Operations Center (SOC): Definition, Types, and Functions
A security operations center (SOC), also known as an information security operations center (ISOC), is a 24/7/365 in-house or external team of IT secu...
READ MOREWhat are The Most Basic Elements of a Strong Cyber Security Posture are?
Cyber security is a complex field that requires careful consideration and planning. It is important to understand the most basic elements of a strong cybersecurity posture in order to ensure the safety of your organization’s data, systems, and networks. The most basic elements include: authentication, authorization, encryption, risk assessment and management, patching and updating software regularly, monitoring for suspicious activity or threats, and disaster recovery plans. By understanding these elements and implementing them into your organization’s security policies you can ensure that your data remains safe from malicious actors.
How To Start To Create a Cyber Security Plan?
Creating a comprehensive cyber security plan is essential for any business. But it can seem daunting to the uninitiated. However, taking the right steps and having an understanding of the basics of cyber security can help you create a strong security plan that will protect your business from potential threats. This blog section outlines the key components of creating a successful cyber security plan and how to get started.