Navigating the Cybersecurity Maze in the Age of AI
February 15, 2024, 19 min read
In the ever-evolving digital world, cybersecurity is no longer a luxury but a necessity. As we dive into the intricate web of online interactions, the shadows cast by cyber threats grow longer and more ominous. This article serves as a beacon, guiding readers through the murky waters of cyber threats to help them navigate the cybersecurity maze. Our journey begins with AI and exploring the current cyber threat landscape, a terrain that is as diverse as it is dynamic.
Cybersecurity in the AI Age
The dawn of artificial intelligence (AI) has brought incredible advancements and daunting challenges, particularly in the realm of cybersecurity. Understanding and navigating the cybersecurity maze in the age of AI is becoming increasingly important for individuals and organizations alike. Cybersecurity is not just about safeguarding against malicious hackers but also about understanding how AI can attack and defend digital assets. AI-driven attacks have the potential to be faster, more efficient, and harder to detect than ever before, making old defense mechanisms potentially obsolete.
Conversely, AI technologies offer new methods to bolster cybersecurity efforts. Machine learning algorithms can now predict and identify potential threats with greater accuracy, providing an essential tool for preemptive defense. However, integrating AI into cybersecurity strategies also introduces complex ethical considerations. Questions arise around privacy, the potential for biased algorithms, and the control of AI decision-making. These are technical issues and involve policy and governance, demanding a multidisciplinary approach to cybersecurity.
The Role of AI in Modern Cyberthreats
AI is a double-edged sword in the mind-blowing world of cyber threats. On the one hand, cybercriminals are utilizing AI to automate attacks, develop sophisticated malware, and execute phishing campaigns that are tougher to identify as they become intricately tailored to mimic legitimate communications. There are AI systems that can learn and adapt to security measures over time, enabling them to find new vulnerabilities and exploit them without human intervention. This shows a drastic shift in the digital security landscape, requiring stakeholders to constantly update their knowledge and tools for protection in this ongoing cat-and-mouse game.
Moreover, data exploitation through AI can lead to severe breaches and unprecedented scales of identity theft, financial fraud, and espionage. Despite the grim outlook, it’s not all doom and gloom. Implementing AI technologies in cybersecurity efforts promises to detect and counter complex threats more effectively than traditional means. Real-time analysis of vast networks and automated responses to security incidents can significantly reduce the window of vulnerability that attackers exploit. Therefore, understanding the role of AI is crucial in crafting advanced cybersecurity strategies.
Artificial Intelligence in Cyber Defense
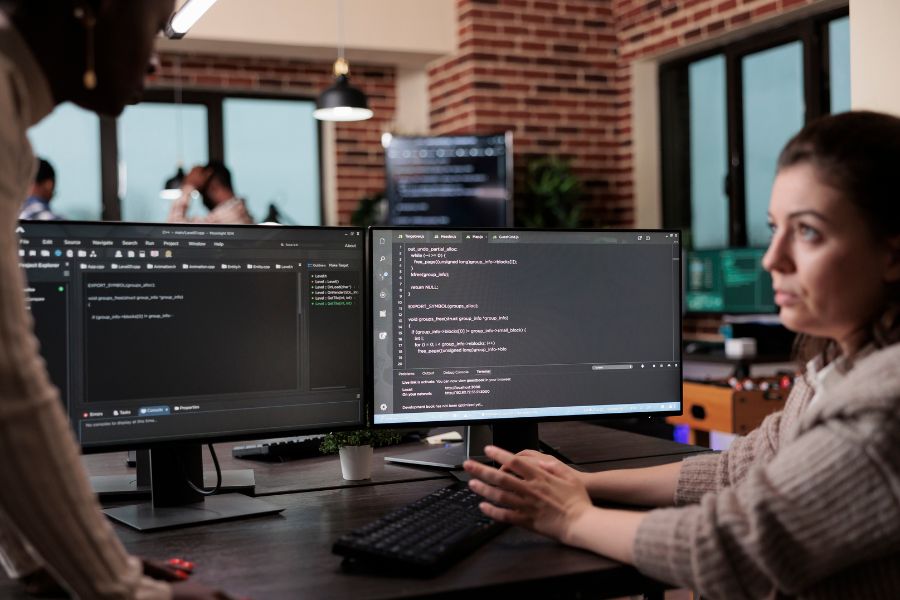
As much as AI presents new threats, it is also an invaluable ally in the fight against cybercrime. AI-driven cybersecurity systems are capable of constant vigilance, monitoring networks for unusual patterns that suggest a breach. These systems can process the data at an astonishing rate, allowing for quick detection and response to various threats. Furthermore, AI’s predictive capabilities mean it can help anticipate attacks before they happen, using historical data to inform security postures. Tailoring AI systems to individual network environments enhances their effectiveness, allowing them to distinguish between usual behavior and genuine threats more precisely.
AI’s challenges to cybersecurity are matched by its potential to innovate and bolster defenses. By leveraging AI, cybersecurity professionals can stay ahead in predicting and mitigating potential attacks. Moreover, AI-driven cybersecurity ensures a dynamic defense that evolves as new threats emerge, utilizing continuous learning to improve over time. Undoubtedly, AI has become a crucial component of effective cybersecurity strategies, representing a paradigm shift in how we protect our digital infrastructures. Embracing AI in cybersecurity is not an option but necessary to secure our interconnected digital world against ever-evolving threats.
Importance of Understanding Attack Type
In this era of ubiquitous digital presence, ignorance is not bliss; it’s a vulnerability. Comprehending the nature of different cyber attacks is the first step in developing a robust defense mechanism. Awareness is the key, whether it’s a large corporation safeguarding its assets or an individual protecting personal information.
However, knowledge alone isn’t sufficient. The practical application of this knowledge through effective detection and mitigation strategies forms the crux of cybersecurity. This article aims not just to enlighten but also to empower. By dissecting various common attacks – their methods, their impacts, and the best strategies to counter them – we equip ourselves with the tools needed to defend our digital frontiers.
Below, we will explain specific attacks, dissect their anatomy, and explore the defenses at our disposal. From the technicalities of SQL injections to the psychological underpinnings of phishing, we will navigate the complex maze of cyber threats together. Our journey is not just about understanding what lurks in the shadows but also about learning how to shine a light on them and render them powerless.
Denial of Service (DoS) and Distributed Denial of Service (DDoS) Attacks
Denial of Service (DoS) and Distributed Denial of Service (DDoS) attacks pose significant cybersecurity threats. These tactics flood targeted systems with overwhelming traffic, rendering them inaccessible to legitimate users. While DoS attacks originate from a single source, DDoS attacks harness multiple compromised devices coordinated by malicious actors. Their impact can be severe, leading to financial losses and reputational damage. Mitigating these threats is crucial in safeguarding against cyber disruptions.
Types and Characteristics
Imagine a bustling marketplace, vibrant and efficient. Now, picture a scenario where this marketplace is suddenly overwhelmed by an influx of crowds, not there to transact but to create chaos. This analogy aptly describes a Denial of Service (DoS) attack. In essence, a DoS attack attempts to disrupt the regular traffic of a targeted server, service, or network by overwhelming the target or its surrounding infrastructure with a flood of Internet traffic.
When this attack comes from multiple sources, it’s a Distributed Denial of Service (DDoS) attack. Like a horde of locusts descending on a field, DDoS attacks are relentless and can originate from a botnet – a network of compromised computers controlled by an attacker. The simplicity yet effectiveness of these attacks make them a favorite among cybercriminals, posing a significant threat to organizations and individuals alike.
Security Solutions and Best Practices
In the face of such threats, defense strategies must be as dynamic as the attacks. Implementing robust firewalls and intrusion prevention systems (IPS) is the first defense line. These tools can help identify and mitigate large-scale traffic before it overwhelms the system. Additionally, employing a content delivery network (CDN) can distribute the load, thereby diluting the impact of an attack.
Best practices also include proactive planning. Regularly updating and patching networked systems ensure that vulnerabilities are not exploited. Moreover, creating a response plan for potential DoS or DDoS attacks ensures preparedness, minimizing potential damage and downtime.
Effective Detection Techniques
Detecting a DoS or DDoS attack early is crucial. Monitoring network traffic and setting thresholds for alerts can provide early warning signs. Unusual spikes in traffic or an influx of requests from a single source or multiple sources with similar characteristics might indicate an impending attack. Employing network monitoring tools that use anomaly detection algorithms can also be instrumental in identifying patterns that deviate from the norm.
Strategies for Mitigation
Once an attack is detected, swift action is required. This may involve re-routing traffic, temporarily null-routing the affected IP address, or even seeking the assistance of your Internet service provider (ISP) for mitigating the attack upstream. It’s also essential to keep communication channels open with stakeholders, informing them of the issue and the steps being taken to resolve it.
Real-World Examples
History has shown us several instances where DoS and DDoS attacks have crippled organizations. From taking down significant websites to disrupting the services of online platforms, these attacks can have devastating effects. By studying these incidents, we can glean insights into the evolving nature of these threats and better prepare for future onslaughts.
Man-in-the-Middle (MitM) Attacks
After exploring the chaos of DoS and DDoS attacks, we now turn to a more surreptitious threat: the Man-in-the-Middle (MitM) attack. Imagine a conversation where a third party secretly intercepts and possibly alters the communication without the participants’ knowledge. That’s the essence of a MitM attack in the digital world. These attacks occur when an attacker secretly relays and possibly alters the communication between two parties who believe they are directly communicating with each other.
The vulnerability exploited here is the lack of verification of the identities of the entities involved in a communication process. Typical scenarios include eavesdropping on public Wi-Fi networks, DNS spoofing, and session hijacking. The danger of MitM attacks lies in their stealth and potential for significant data breaches.
Security Measures to Prevent MitM
Preventing MitM attacks involves several layers of security. Encryption is the first line of defense; using HTTPS over HTTP, employing VPNs for secure connections, and implementing SSL/TLS protocols are essential steps. Additionally, ensuring proper authentication mechanisms, like multi-factor authentication, can significantly reduce the risk of such attacks.
Organizations should also educate their employees and users about the risks of unsecured networks, especially public Wi-Fi, and the importance of regularly updating software to patch any security vulnerabilities.
Detection Methods
Detecting a MitM attack requires vigilance and the right tools. Monitoring for unexpected certificate authority certificates and sudden changes in network performance can signal an ongoing MitM attack. Network security tools that can analyze traffic patterns and identify anomalies play a crucial role in early detection.
Mitigation Approaches
Upon detecting a MitM attack, immediate action is required to secure the communication channels. This may involve disconnecting compromised sessions, changing passwords and security certificates, and conducting a thorough security audit to understand the extent of the breach. Continuous monitoring and updating of security protocols is crucial in preventing future attacks.
Case Studies
Real-world examples of MitM attacks highlight their potential impact. From financial institutions to social media platforms, no sector is immune. Analyzing these cases provides valuable insights into the methods used by attackers and the steps taken by organizations to mitigate the damage.
Packet Sniffing
Packet sniffing, a technique used in network security, involves intercepting and monitoring data packets as they travel across a network. This method allows an attacker to capture sensitive information transmitted over the network, such as login credentials, personal data, or financial details. By analyzing these packets, malicious actors can exploit vulnerabilities and gain unauthorized access to systems or compromise user privacy. Effective encryption and secure network protocols are essential countermeasures to mitigate the risks associated with packet sniffing.
Types of Packet Sniffing Techniques
Cyber espionage involves capturing packets of data as they traverse a network. The danger lies not in the mere interception but in extracting and exploiting sensitive information from these packets. Packet sniffing can be either passive, quietly collecting data without altering it, or active, where the sniffer might manipulate or send packets.
Understanding the types of packet sniffing and their operational methods is crucial for identifying vulnerabilities in a network and implementing effective security protocols.
Security Solutions for Prevention
Encryption is again a key player to guard against packet sniffing. Encrypting data in transit ensures that the information within remains unintelligible even if packets are intercepted. Implementing secure protocols like HTTPS, SSL/TLS, and VPNs for sensitive communications is a fundamental practice.
Additionally, network segmentation and intrusion detection and prevention systems (IDPS) can limit the reach and impact of a sniffer within a network. Regularly monitoring network traffic for unusual patterns is also vital for early detection of potential sniffing activities.
Detection and Monitoring Methods
Detecting packet sniffing involves monitoring network traffic for signs of interception. Tools that analyze packet flows and detect anomalies can help in identifying unauthorized sniffers. Regular network audits and the use of anti-sniffing tools can also reveal the presence of packet sniffing activities.
Mitigating the Impact
In the event of a sniffing attack, immediate measures include isolating the affected segments of the network, changing credentials and security certificates, and conducting a thorough investigation to assess the breach’s extent. Educating network users about secure communication practices and regularly updating software and hardware components are also crucial steps in mitigating the risks associated with packet sniffing.
Examples from the Field
Real-life incidents of packet sniffing have ranged from corporate espionage to large-scale data breaches. By examining these cases, we can better understand the methods used by attackers and refine our defense strategies accordingly.
Port Scanning
Transitioning from the covert nature of packet sniffing, we delve into another attacker reconnaissance technique: Port Scanning. This method involves probing a server or network to identify open ports and services, essentially finding doors that might be unlocked. While port scanning isn’t malicious, it is often the precursor to more sinister activities, serving as a roadmap for attackers to identify potential vulnerabilities.
Understanding how port scanning works in the cybersecurity chess game equips us to secure our network’s ‘entry points better’ and anticipate potential attack strategies.
Security Solutions and Protection
The first step in safeguarding against port scanning is to minimize the number of open ports. This can be achieved by ensuring that only essential services are running and accessible. Employing firewalls effectively to shield ports and services that need to remain open is also crucial. Firewalls configured to detect and block unauthorized port scans add a layer of defense.
Regularly updating and patching software and operating systems to address known vulnerabilities can deter attackers from exploiting outdated systems through open ports.
Detection Strategies
Detecting port scanning activities involves monitoring network traffic for patterns that indicate scanning, such as many connection requests to different ports in a short period. Intrusion detection systems (IDS) and network monitoring tools are vital in identifying these scanning activities, allowing for timely defensive actions.
Mitigation Tactics
Upon detecting a port scan, immediate actions include reviewing firewall configurations and ensuring that all non-essential ports are closed or protected. Enhancing monitoring and alert systems to react to future scans more effectively is also crucial. In some cases, engaging with network or cybersecurity professionals to conduct a thorough security audit may be necessary to identify and address overlooked vulnerabilities.
Incident Examples
Examining real-world examples of breaches that began with port scanning can be enlightening. These incidents often highlight the importance of vigilance and proactive network management in preventing larger-scale attacks.
SQL Injection
Building on the understanding of reconnaissance techniques like port scanning, we now turn to a more direct form of attack: SQL Injection. This attack exploits vulnerabilities in a website’s database management system. Attackers use malicious SQL code for backend database manipulation to access information not intended to be displayed. This includes sensitive company data, user personal information, and more. SQL Injection can be as harmful as leaving the door open for attackers to rummage through your digital belongings.
Understanding SQL Injection is crucial in a world where data is king, and protecting that data is paramount to maintaining trust and integrity in digital interactions.
Security Solutions for SQL Injection
The primary defense against SQL Injection involves validating and sanitizing all user input. This means rigorously checking the data provided by users before the database processes it. Employing prepared statements with parameterized queries is also practical, as it separates SQL code from data inputs.
Moreover, regularly updating and patching web applications and databases can close off vulnerabilities that SQL Injection attacks could exploit.
Detection Techniques
Detecting SQL Injection typically involves monitoring for unusual database activity or errors that indicate a manipulation attempt. Web application firewalls (WAF) can be configured to detect and block SQL Injection attacks by identifying malicious SQL queries.
Mitigation Strategies
Once an SQL Injection has been identified, immediate steps include isolating the affected database, reviewing and cleansing any compromised data, and patching the exploited vulnerability. Conducting a thorough security audit to assess and improve the overall security posture of the web application is also essential.
Real-Life Incidents
Real-life examples of SQL Injection attacks demonstrate their potential to cause significant harm to organizations and individuals. By studying these incidents, we gain insights into common vulnerabilities and the best practices for prevention and response.
Cross-Site Scripting (XSS) and Cross-Site Request Forgery (CSRF)
Cross-Site Scripting (XSS) and Cross-Site Request Forgery (CSRF) are significant security vulnerabilities in web applications.
XSS involves injecting malicious scripts into web pages viewed by other users. These scripts can steal sensitive data, manipulate page content, or perform unauthorized actions on behalf of the user.
CSRF, conversely, tricks authenticated users into executing unwanted actions on a web application where they are already authenticated. Attackers craft malicious requests and trick users into unknowingly submitting them, leading to actions like changing account settings, transferring funds, or making purchases without the user’s consent.
Types and Risks
Building on web-based vulnerabilities, such as those exploited by SQL Injection, we now explore the realms of Cross-Site Scripting (XSS) and Cross-Site Request Forgery (CSRF). These attacks target the users of web applications rather than the applications themselves. XSS occurs when attackers inject malicious scripts into web pages viewed by other users, potentially leading to stolen data, hijacked sessions, or malicious redirection. CSRF tricks a user’s browser into executing unwanted actions in a web application where they are authenticated, exploiting a site’s trust in the user’s browser.
XSS and CSRF expose the intricate nature of web security, where exploiting the trust and interconnectivity of web applications and users can lead to significant breaches. To mitigate these risks and protect users ‘ data, web developers must implement proper security measures such as input validation, output encoding, and anti-CSRF tokens.
Preventive Security Solutions
To combat XSS, proper input validation, output encoding, and the use of appropriate web frameworks that automatically handle these protections are key. Additionally, implementing a Content Security Policy (CSP) can help in preventing the execution of malicious scripts.
For CSRF protection, one effective strategy is using anti-CSRF tokens in web forms, ensuring that only requests from the site’s forms are accepted. Regularly updating and patching web applications also play a crucial role in mitigating these threats.
Detection and Response
Detecting XSS and CSRF involves monitoring for unusual patterns in web traffic and user behavior. Web Application Firewalls (WAF) can be configured to detect and prevent both XSS and CSRF attacks by inspecting HTTP requests and responses for malicious patterns.
Mitigation Best Practices
Upon detection of XSS or CSRF, immediate steps should include purging malicious scripts, invalidating affected sessions, and conducting a thorough audit to identify and patch the vulnerabilities exploited. Educating users about the importance of security practices, like not clicking on suspicious links, is also vital.
Notable Examples
Real-world incidents involving XSS and CSRF have highlighted the importance of robust web application security. These examples serve as cautionary tales, illustrating the potential damages and reinforcing the need for vigilant security measures.
Cybersecurity is not a static field but a continuous journey. Vigilance, adaptation, and education are essential. Regular security audits, proactive threat detection, and a comprehensive incident response plan are crucial in navigating the cyber threat landscape.
Phishing Attacks
Phishing attacks are deceptive tactics cybercriminals use to trick individuals into divulging sensitive information such as login credentials, financial details, or personal information. Typically, phishing attacks involve fraudulent emails, messages, or websites that mimic legitimate entities, such as banks, social media platforms, or government agencies. These fake communications often contain urgent requests or enticing offers to lure victims into clicking on malicious links, downloading harmful attachments, or providing their confidential information. Once obtained, this information can be used for identity theft, financial fraud, or unauthorized account access. Vigilance, skepticism, and awareness of phishing techniques are crucial in preventing falling victim to these attacks.
Variants of Phishing
As we move from specific web application attacks like XSS and CSRF, we now focus on a more direct form of deception: Phishing. This prevalent cyber attack deceives individuals into providing sensitive data, such as login credentials or credit card numbers, by masquerading as a trustworthy entity in electronic communications. Phishing can take various forms, from emails impersonating legitimate businesses to spoofed websites that appear authentic. The evolution of phishing techniques, including spear phishing targeting specific individuals and whaling aimed at high-profile targets, highlights the adaptive nature of this threat.
Understanding the various forms of phishing is critical in a digital age where information is a valuable currency, and its protection is paramount.
Security Measures Against Phishing
The best defense against phishing is awareness and education. Users should be trained to recognize the signs of phishing attempts, such as unsolicited requests for sensitive information, and to verify the authenticity of messages and websites. Technical measures include using email filters to detect and block phishing emails and implementing two-factor authentication to add an extra layer of security against compromised credentials.
Regularly updating security software to protect against malware often associated with phishing attacks is also essential.
Detecting Phishing Attempts
Effective detection of phishing attempts hinges on vigilance and an understanding of common phishing indicators. Unusual sender addresses, misspelled URLs, and unexpected requests for sensitive information are red flags. Organizations can employ advanced email security solutions that utilize machine learning to identify and filter out phishing emails more effectively.
Mitigation and User Education
In the event of a phishing attack, immediate actions include changing compromised passwords and monitoring for unauthorized activities. Educating users about safe browsing practices and how to report suspected phishing attempts is crucial for preventing future incidents.
Case Studies
Analyzing real-world phishing attacks reveals their methods and impacts, offering valuable lessons in continuous vigilance and proactive security measures.
DNS Spoofing and Cache Poisoning
After discussing the human-focused tactics of phishing, we now pivot to a more technical subterfuge: DNS Spoofing and Cache Poisoning. These attacks target the Domain Name System (DNS), which translates website names into IP addresses. In DNS Spoofing, attackers divert traffic from legitimate sites to fraudulent ones by corrupting the DNS resolution process. Cache Poisoning, a subset of DNS Spoofing, involves inserting false information into the DNS cache so users are redirected to malicious sites without their knowledge.
These attacks exploit the trust users place in internet navigation, making them insidious. They can lead to significant data breaches, the spreading of malware, and the undermining of user confidence in online systems.
Security Solutions
Implementing DNS security extensions (DNSSEC) is vital to combat these threats. DNSSEC adds a layer of authentication to the DNS process, ensuring that the information received is from a legitimate source. Additionally, using secure and updated DNS servers, regularly clearing DNS cache, and employing network security tools that monitor and validate DNS traffic can help mitigate these risks.
Detection Mechanisms
Detecting DNS Spoofing and Cache Poisoning involves monitoring for unexpected redirections and anomalies in DNS responses. Network security solutions that analyze DNS traffic for signs of tampering play a crucial role in identifying these attacks.
Mitigation Techniques
Upon detecting DNS tampering, immediate action should include isolating the affected systems, purging poisoned DNS caches, and switching to secure DNS servers. Conducting a thorough investigation to identify the source of the attack and patching any discovered vulnerabilities are also critical steps.
Example Scenarios
Real-life incidents of DNS Spoofing and Cache Poisoning demonstrate the disruptive potential of these attacks. Examining these cases provides insights into attack methodologies and reinforces the need for robust DNS security measures.
Eavesdropping Attacks
As we navigate from the complexities of DNS Spoofing and Cache Poisoning, we encounter another clandestine threat: Eavesdropping Attacks. These attacks involve unauthorized interception of private communications. Unlike the more direct nature of DNS attacks, eavesdropping is about silently listening in, gathering information without altering it or alerting the victims. These attacks can occur in various forms, including network eavesdropping, where attackers capture unsecured network traffic, and acoustic eavesdropping, where physical conversations are overheard.
Eavesdropping poses a significant risk as it can expose sensitive information, personal data breaches, and corporate espionage.
Security Solutions for Eavesdropping
Encryption is key to safeguard against eavesdropping. Encrypting data in transit and at rest ensures that intercepted information remains confidential. For network security, using VPNs, especially on public networks, provides an additional layer of protection. Regarding physical security, controlled access to sensitive areas and sound masking are practical measures against acoustic eavesdropping.
Detection and Prevention
Detecting eavesdropping can be challenging due to its covert nature. However, monitoring network traffic for unusual patterns and implementing intrusion detection systems can help identify potential eavesdropping. Regular security audits and employing anti-eavesdropping measures, such as bug sweeps, are also important.
Mitigation Strategies
Upon suspicion or detection of eavesdropping, immediate actions include changing communication methods, strengthening encryption protocols, and conducting a thorough investigation to identify any security lapses. Educating employees about secure communication practices and the risks of eavesdropping is also crucial.
Example Cases
Studying real-world cases of eavesdropping attacks reveals the extent of their potential damage and underscores the need for robust security measures in both digital and physical realms.
Zero-Day Exploits
Following the discussion of eavesdropping, representing a stealthy and often unnoticed threat, we now focus on a similarly insidious yet technologically oriented danger: Zero-Day Exploits. These attacks target vulnerabilities in software or hardware unknown to those interested in mitigating the vulnerability, including the vendor of the target software. The term “zero-day” refers to the developers having zero days to fix the issue since it’s already been exploited. Cybercriminals highly prize these vulnerabilities and can be used to create powerful malware and targeted attacks.
The threat posed by zero-day exploits lies in their unpredictability and potential for significant damage before detection and patching.
Security Solutions and Preparedness
Protecting against zero-day exploits involves a multi-layered approach. Traditional antivirus software might be ineffective since these vulnerabilities are unknown until exploited. Emphasizing on threat intelligence, behavioral-based detection systems, and deploying advanced intrusion detection systems are crucial. Regularly updating systems and software can mitigate the risk as patches are released.
Adopting a proactive cybersecurity posture, including regular security audits and a robust incident response plan, is essential in preparing for potential zero-day attacks.
Detection and Early Warning Systems
Early detection of zero-day exploits is challenging but not impossible. Employing advanced security solutions that focus on behavioral anomalies rather than signature-based detection is key. Network monitoring tools and AI-driven threat detection systems can provide early warnings of suspicious activities indicative of a zero-day exploit.
Mitigation Techniques
Upon identifying a potential zero-day attack, immediate action includes isolating affected systems, conducting a thorough forensic analysis to understand the exploit, and implementing emergency patches or workarounds. Communication with software vendors for patches and sharing information with the cybersecurity community are vital steps.
Historic Zero-Day Exploits
Exploring historical instances of zero-day exploits provides valuable lessons in the evolution of these threats and the importance of staying ahead in the cybersecurity arms race.
Spectrum of Cyber Threats in the Age of AI
As you can see above, the spectrum of cyber threats in the age of AI is vast. Each attack has its unique fingerprint; understanding these nuances is crucial in fortifying our digital defenses. And the bad part is we even don’t list all of them. The landscape is constantly shifting, and threats are becoming more sophisticated, with new threats emerging as swiftly as old ones are neutralized. Staying abreast of these developments is not just a matter of keeping up with the times; it is an essential strategy for survival in the digital age. Cyber threats are constantly evolving, with each attack method presenting unique challenges. Awareness and understanding of these threats are the first steps toward effective defense.
Conclusion
Looking ahead, the cybersecurity landscape will continue to change. The rise of technologies like artificial intelligence and machine learning presents new opportunities for both security enhancement and potential exploitation. Staying informed about emerging threats and evolving security solutions is vital.
The increasing interconnectedness of digital systems also highlights the importance of collaborative security efforts. Sharing knowledge and resources within the cybersecurity community can strengthen collective defenses against common threats.
The diversity of attacks we’ve discussed underscores the need for a multi-faceted approach to cybersecurity. This includes maintaining up-to-date systems, employing robust security protocols, and fostering a culture of security awareness within organizations. By understanding the cyber threats, staying informed about advancements in security technology, and fostering a proactive security culture, individuals and organizations can better protect themselves in the digital world.
Recommended Reading: Dark Reading